A Deep Dive into Zero-Day Vulnerability Alerts with New Relic APM
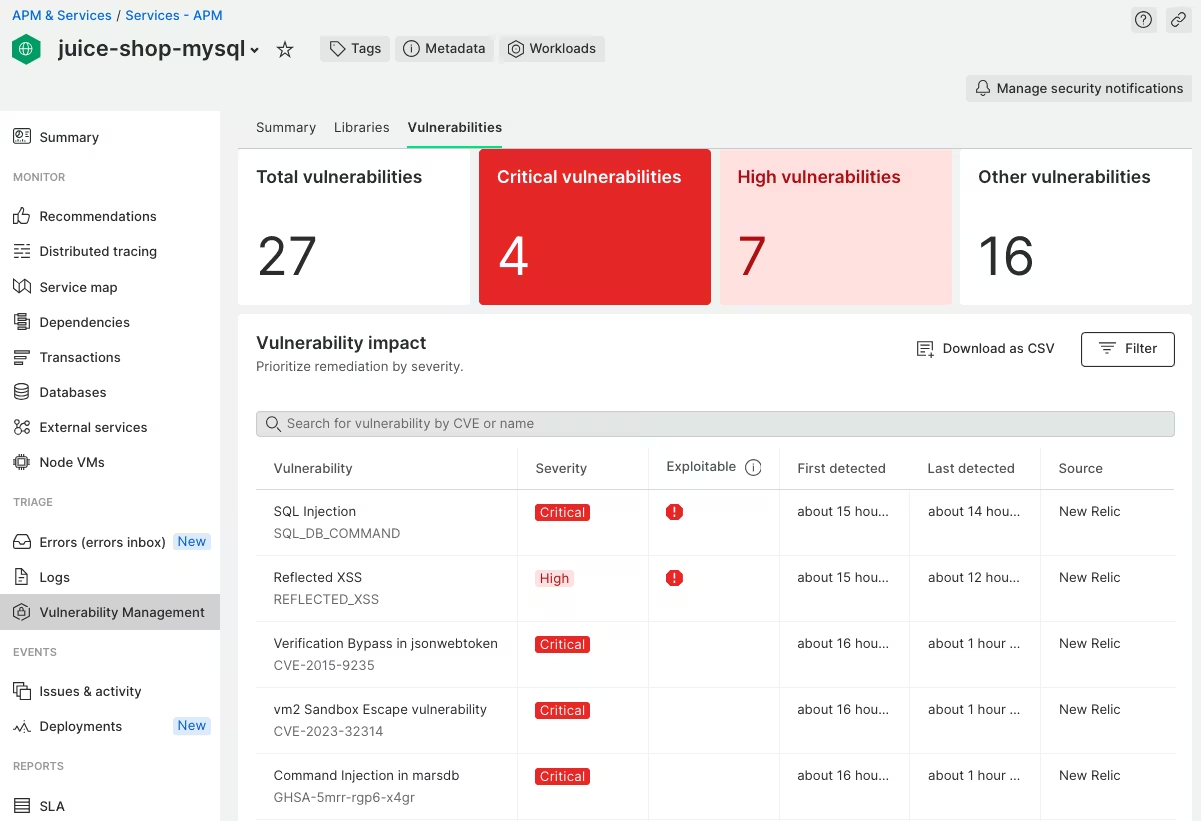
Empowering Developers with Real-Time Security Insights and Proactive Vulnerability Management Amidst the ever-evolving landscape of cybersecurity, the recent revelation of a zero-day vulnerability in Fortinet’s FortiOS serves as a stark reminder of the constant cat-and-mouse game between defenders and attackers. Staying ahead of potential security threats isn’t just a best practice; it’s a necessity. For developers, the challenge lies not only in identifying vulnerabilities but in doing so proactively, especially when it comes to zero-day exploits. In this blog post, we’ll explore how New Relic application performance monitoring (APM) empowers developers to create zero-day vulnerability alerts, offering a robust solution to enhance security postures without the need for extensive scanning. ...